Codility Beta Challenge - Number Of Disc Intersections
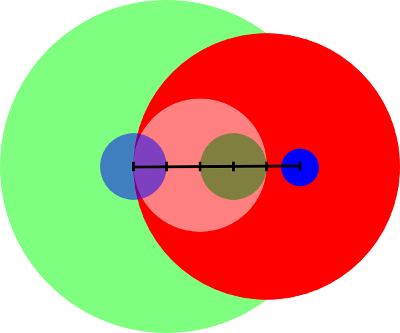
This challenge on Codility is an interesting one: given a number of disks of various radii distributed over a line, can you count the total number of intersections in O(N·log(N))?
Here’s an example:
To have a clear idea of how to solve this, I...
Read more »iCTF 2011 - challenges writeup
Hello people! The International Capture The Flag hacking competition iCTF 2011, the biggest CTF so far, is over, and it’s time for writeups! Here’s the solutions of the challenges I wrote. Hope you enjoyed them
I Read It Encoded: Challenge, 50 dirty...
Read more »DEFCON quals 19 - Pwtent Pwanble 200 writup
Here’s how we solved the pp200 challenge, with the Shellphish team (by Manuel, Johannes, Don and I).
For this challenge, we were given an address/port and a file, which was a Solaris executable. Opened in IDA, the executable turned out to be a simple...
Read more »Debugging a leaky Python
Python 2.6, the one that’s probably sitting in your hard disk, has a reference counting garbage collector. That means that objects are removed from memory right away if there is no object that is referencing them any more.
To avoid leaks, you should...
Read more »